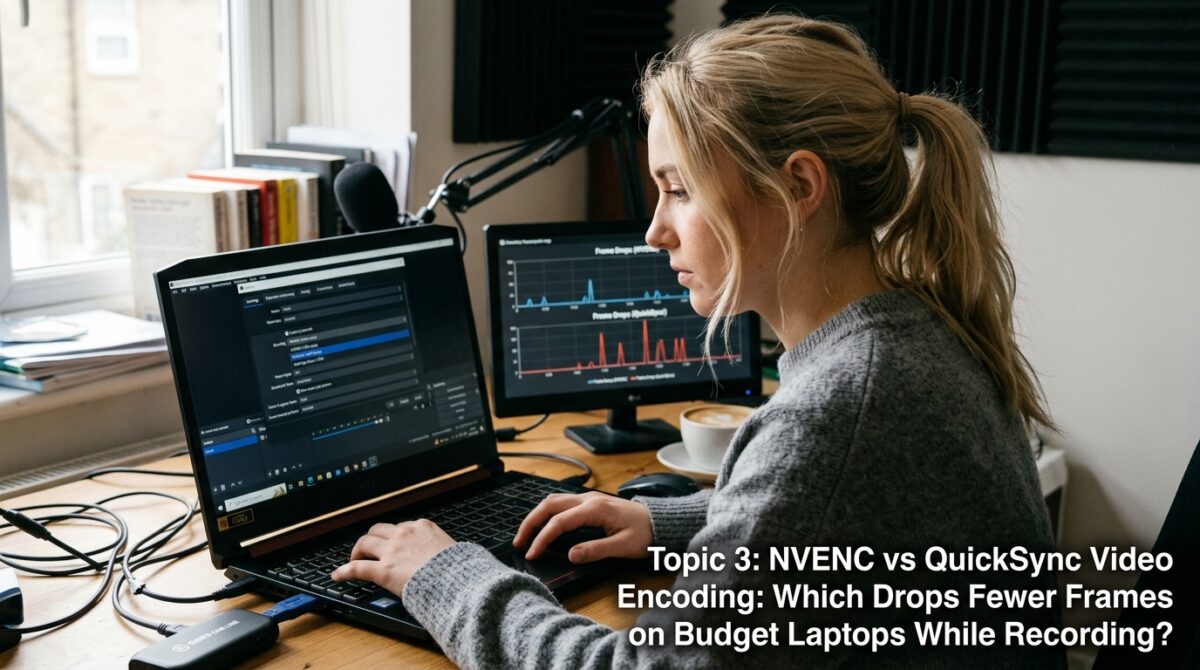
NVENC vs QuickSync Video Encoding: Which Drops Fewer Frames on Budget Laptops While Recording?
When attempting to maintain smooth performance while encoding video in real time, recording games or screen activity on a budget laptop may sometimes push the hardware to its limits. This is particularly true when the goal is to record the action on the screen. The possibility of missing frames becomes increasingly obvious as video resolutions and bitrates grow. This has an impact on both the quality of the recording and the smoothness of the playback. NVENC and QuickSync are two hardware encoders that are extensively used for this purpose. Both of these encoders are intended to offload encoding chores from the central processing unit (CPU). There is a substantial difference in their underlying designs and the way they use resources, despite the fact that both attempt to enhance efficiency. These distinctions become much more important when considering laptops with lower-end specifications, which have lesser levels of CPU power, GPU performance, and thermal capacity. When selecting the appropriate encoder, it is possible to decide whether recordings undergo stuttering and frame loss or if they stay steady. To arrive at the best choice, it is essential to have a solid understanding of how each technology operates when applied to real-world scenarios.
Learning How NVENC Operates on Low-Cost Laptops
In NVIDIA graphics processing units (GPUs), NVENC is a specialized hardware encoder that was developed exclusively for the purpose of video encoding activities. Not like software encoding, it uses a separate fixed-function unit to work independently of the central processing unit (CPU) and the majority of the GPU cores. Furthermore, this enables NVENC to encode video with a little effect on the performance of the system, which is particularly advantageous while gaming or doing many tasks at the same time. This separation helps preserve smoother frame rates when filming on cheap laptops that have graphics processing units (GPUs) that are entry-level. On the other hand, NVENC continues to share graphics processing unit (GPU) power and thermal constraints, which means that excessive GPU utilization might indirectly influence encoding stability. In the event that the graphics processing unit (GPU) overheats and slows down over longer sessions, there is a possibility that there may be a little decrease in performance; nevertheless, in general, it continues to be efficient and consistent.
Acquiring Knowledge about the Intel QuickSync Technology
The QuickSync software is a hardware-accelerated video encoding solution developed by Intel that is included into the graphics unit that is built into the CPU. In order to perform encoding and decoding operations, it makes use of a media engine that is specifically part of the CPU package. Consequently, it is more efficient than conventional software encoding since it is able to operate without primarily depending on the primary cores of the central processing unit. When the graphics processing unit (GPU) of a low-cost laptop is under severe demand or when there is no specialized GPU available, QuickSync may be an especially beneficial feature. On the other hand, due to the fact that it shares system memory and power restrictions with the central processing unit (CPU), its performance might vary based on the overall utilization of the system. QuickSync may experience resource contention when the central processing unit (CPU) is juggling many activities, which might have an effect on the recording stability.
Behavior During Recording Sessions That Involves Dropping Frames
Frame drops are a common occurrence that occur when the system is unable to deal with the demands of encoding in real time. As a result of the use of a specialized encoder that does not directly compete with CPU duties, NVENC has a tendency to generate a lower number of lost frames. Because of this separation, the system is able to keep the encoding performance stable even when the central processing unit is doing a lot of work. QuickSync, on the other hand, is susceptible to fluctuations due to the fact that it is dependent on shared resources inside the central processing unit (CPU) and integrated graphics. When the system is operating with a large number of apps, the performance of the encoding process may decrease, which may result in occasional frame dropouts. When it comes to inexpensive laptops, when hardware resources are already restricted, this discrepancy becomes much more noticeable for the user.
Differences in the Resource Allocation Between the CPU and GPU
The manner in which NVENC and QuickSync make use of the resources available on the system is one of the most significant differences between the two. NVENC transfers all of the encoding to the specialized hardware block of the GPU, which frees up the central processing unit is resources for use in other activities, such as game logic or background functions. This is especially helpful in gaming situations when the amount of headroom available on the CPU is essential. QuickSync transfers the burden to the inbuilt graphics processing unit (GPU), which shares resources with the central processing unit (CPU). Despite the fact that this may lessen the stress on the GPU, it requires more power from the CPU and more bandwidth from memory. This shared resource approach has the potential to cause bottlenecks on budget systems, particularly in situations when numerous processes are carrying out their tasks concurrently.
Thermal Performance and Other Effects Related to Throttling
When it comes to inexpensive laptops, thermal constraints are a key worry since these laptops often have cooling systems that are less sophisticated. The GPU may throttle in order to maintain safe temperatures when subjected to persistent workloads, and NVENC is a contributor to GPU heat. NVENC, on the other hand, has a very mild thermal effect in comparison to full GPU workloads. This is due to the fact that it is efficient. The increased activity of the central processing unit (CPU) and integrated graphics processing unit (GPU) that QuickSync causes might result in greater temperatures for the CPU. If the central processing unit (CPU) becomes too hot, it may slow down, which will have an impact not only on the encoding process but also on the overall performance of the system. The workload of NVENC is more separated from the CPU, which allows it to maintain a more steady performance over time. This is the case in many instances.
Efficiency of Data Flow and Memory Bandwidth respectively
When it comes to real-time video encoding, efficient data processing is very necessary. Rather of transferring data across system memory, NVENC processes frames directly on the graphics processing unit (GPU). By streamlining the procedure, we are able to maintain constant performance and reduce latency. It is common for QuickSync to need the transfer of frames between the discrete GPU, the system memory, and the integrated GPU. This is dependent on the configuration of the system. This supplementary data transfer has the potential to cause delays and use bandwidth, which is especially obvious on systems that have slower memory. It is possible for this overhead to contribute to frame dips during high-resolution recording on budget laptops, which have restricted memory speed and bandwidth.
Performance under Real-World Conditions on Low-Cost Hardware
In real-world situations, NVENC often provides a recording performance that is more consistent and smoother on low-cost laptops that are equipped with NVIDIA graphics processing units by default. Because of its specialized hardware architecture, it is able to perform encoding in an efficient manner without having a significant influence on other components of the system. During times of lesser workloads or when the system is not being highly taxed, QuickSync functions quite well; nevertheless, its performance might fluctuate when it is under stress. Despite the fact that QuickSync has made substantial advancements on more recent CPUs, it still has a tendency to be more sensitive to the total load on the system in comparison to NVENC. NVENC often offers a more consistent experience for those who are capturing games or video with a high bitrate.
Which Encoder Loses a greater number of frames overall?
When it comes to recording, NVENC often loses less frames than QuickSync does, particularly in intensive situations such as gaming or multitasking. QuickSync, on the other hand, causes more frames to drop when recording. When it comes to ensuring constant frame delivery, it has a distinct edge because to its dedicated hardware encoder, less dependence on CPU resources, and fast data processing. QuickSync continues to be a powerful option for computers that do not have specialized graphics processing units (GPUs) or for recording jobs that are not as heavy; nevertheless, it is more prone to performance swings when it is under strain. NVENC is often the preferable option for users that prioritize smooth recordings with little interruptions. It offers more dependability and stability on entry-level hardware, making it possible for users to achieve their goals.